
Master LAMP on Ubuntu 24.04 LTS with our step-by-step installation guide. Perfect for beginners and pros to set up a robust web server effortlessly.

Master LAMP on Ubuntu 24.04 LTS with our step-by-step installation guide. Perfect for beginners and pros to set up a robust web server effortlessly.
Entrepreneurial burnout is a state of physical, emotional, and mental exhaustion caused by prolonged and intense stress associated with running a business. It can lead

Technology plays a pivotal role in modern business management, serving as the backbone for operations, strategic decision-making, and competitive advantage. It streamlines processes, enhances communication,

The Ethics of Artificial Intelligence (AI) encompasses a broad range of moral principles and considerations that arise with the development, deployment, and use of AI
The Rise of Digital Nomadism: Embracing Work from Anywhere In recent years, the concept of remote work has evolved from a rare perk to a

Keto recipes for beginners are designed to ease individuals into the ketogenic diet, a low-carb, high-fat diet that aims to put the body into a
The evolution of cybersecurity is a complex journey that mirrors the advancement of technology and the ever-changing landscape of digital threats. From its rudimentary beginnings

Ensuring data privacy in the cloud involves adopting a comprehensive approach that encompasses both technical measures and adherence to regulatory standards. As organizations increasingly migrate

Understanding Social Commerce Trends In the ever-evolving landscape of digital marketing, social commerce stands out as a transformative trend. Entrepreneurs, particularly those seeking a fresh

The Struggle with Coffee Cutting back on coffee can be particularly challenging for several reasons. First, the caffeine it provides is a much-relied-upon energy boost

Windows Task Manager is akin to a health monitor for your computer, providing insights into the system’s performance, application behavior, and resource usage. Yet, for

Welcome, fellow Linux Administrators! Today, we’re diving into the setup of a robust LAMP stack on AlmaLinux 9.3. The LAMP stack, comprising Linux, Apache, MySQL
When it comes to choosing an operating system for your workstation, the decision often comes down to personal preference, specific job requirements, and familiarity. Two
In the dynamic world of web development and server administration, keeping your software up to date is essential for ensuring security, performance, and compatibility. The
The Power of Social Media Algorithms In today’s digital age, social media algorithms play a pivotal role in determining the visibility and reach of content.

In today’s digital landscape, small businesses have become a prime target for cyberattacks. As technology continues to advance, so do the tactics employed by malicious

Virtualization technology has become an integral part of modern computing, enabling efficient resource utilization and enhanced flexibility. In the Linux world, Kernel-based Virtual Machine (KVM)

Introduction In today’s digital age, an effective Influencer Marketing Strategy can be a game-changer for entrepreneurs looking to revamp their business and personal lives. The

Introduction to Social Media Engagement Social media has become an indispensable tool for business growth across all sectors, providing a platform for direct customer interaction

Connecticut privacy data laws are a critical framework ensuring the protection of personal information within the state. The Connecticut General Statutes, particularly section 743dd, lay

The fall of communism in Eastern Europe and the Soviet Union marks one of the most pivotal events of the 20th century, altering the geopolitical

The concept of the nation-state, once the cornerstone of political and social order in the West, is experiencing a significant transformation. This shift is largely

Globalization is a phenomenon that has had an impact on the fabric of contemporary Western civilization, fostering an interconnected world where boundaries are blurred, and

In the realm of music, some tracks stand out as timeless, leaving an indelible mark on the cultural landscape. Iconic songs like Led Zeppelin’s “Stairway

Responding to a Request for Proposal (RFP) in the IT security sector involves critical assessment and strategic planning. Here, we delve into the nuances of

Responding to a Request for Proposal (RFP) is a critical step in securing a new business project for IT firms. It’s a process that requires

In the realm of data protection, the debate between cloud and legacy backup methods remains pertinent. As businesses generate vast amounts of data, choosing the

In the digital age, investigative efforts often require extracting evidence from an individual’s online activities. One critical avenue is through Internet Service Providers (ISPs). They

In the realm of cybersecurity, understanding and integrating digital forensics into incident response is not just beneficial; it’s essential for comprehensive security management. They go

Voice Over IP (VoIP) technology, while revolutionizing the way we communicate, carries its own set of security challenges. VoIP, akin to any IP-based service, is

Digital Privacy and the Fourth Amendment: Navigating Modern Challenges In today’s digital age, the concept of digital privacy and our Fourth Amendment rights has evolved

In the realm of digital forensics and cybersecurity, Network Traffic Analysis Tools play a pivotal role in unraveling the complexities of network activities. These tools

Mobile Forensics: A Comprehensive Guide Mobile forensics is an essential aspect of modern investigative processes. As mobile phones evolve, becoming more sophisticated and computer-like, the

In the realm of digital forensics, especially on Macintosh systems, the importance of reliable data recovery tools cannot be overstated. Whether files were lost accidentally

In the realm of digital forensics, understanding the nuances between Windows and Macintosh systems is crucial for conducting effective investigations. Despite both being popular operating
Linux forensics is an essential field in cyber security, focusing on extracting and analyzing evidence from Linux systems. This guide highlights vital resources and tools

In the realm of digital forensics, Windows Forensics plays a crucial role, especially in sensitive and complex child pornography cases. The process is rigorous and

The CAN-SPAM Act is a critical piece of legislation that every email marketer should be familiar with. Its rules apply to all email messages used

In an era where network security is paramount, understanding and managing changes within IT environments is critical. Tools like Tripwire and CimTrak are essential for

Windows and Linux, two of the most prevalent operating systems in the world, are fundamentally different yet both are crucial in the realm of digital

Software Configuration Management (SCM): Essential for Project Success Software Configuration Management (SCM) plays a crucial role in tracking and controlling changes in the software development

Exploring the Realm of Data Recovery Data recovery, a critical process for retrieving lost or formatted information, is bound by the principle that successful recovery

Steganography, the art of concealing information within other media, is a double-edged sword, used for both legitimate and illicit purposes. This blog explores essential tools

Steganography, the art of hiding information within other media, carries both beneficial and harmful potentials, depending on its application. This post delves into the ethical

In an era where celebrities often fall prey to cybercrimes, understanding the nuances of forensic investigation is paramount. This article delves into the complexities of

DoS Attacks (Denial of Service), along with their more complex counterparts, DDoS (Distributed Denial of Service) attacks, pose significant threats to online services and platforms.

Setting up a digital forensics lab requires careful consideration of the tools and equipment necessary to conduct thorough and effective investigations. This blog explores the
In the realm of digital forensics, obtaining the right certifications is crucial for career advancement and skill enhancement. This article delves into the most sought-after

In today’s world, where cybercrime is rampant, digital forensics firms play a crucial role in investigating and supporting litigation for various cyber-related incidents. From data

Denial of Service (DoS) attacks are notorious for crippling network resources, denying legitimate users access to services. This post delves into the tools commonly used

In the world of e-commerce, security is paramount. Webmasters face a constant battle against a variety of threats that can compromise their websites and the

In an age where cybercrime is increasingly prevalent, understanding how to report these incidents promptly and to the correct authorities is crucial for personal and

Secure Transactions: The First Step to Online Success Transitioning your business online is a significant leap towards growth, as I learned from my experience transitioning

The discussion around implementing a line-item veto in the federal government highlights a crucial aspect of political reform, aiming to refine the legislative process and

The concept of imposing term limits on members of the federal government has garnered attention as a means to rejuvenate the political landscape of the

The Carpenter v. United States case represents a pivotal moment in the intersection of digital privacy and constitutional law, particularly concerning the Fourth Amendment’s application
The Constitutional right to privacy is a fundamental aspect of American liberty, offering protections against unlawful searches and ensuring personal freedom. The Fourth Amendment: A

In the current digital landscape, safeguarding corporate data is paramount. Public Key Infrastructure (PKI) and encryption are critical tools in this endeavor, ensuring secure communication

Data centers are crucial for storing and managing the vast amounts of data that organizations generate. However, security breaches in these environments can lead to

In the realm of cybersecurity, an effective incident response is critical for mitigating risks and restoring normal operations. However, a recent review of an incident

In the realm of network security, ensuring the safe transmission of data across networks is crucial, especially for remote access. The deployment of encryption technologies

Malware, such as the Backdoor.Hyperbro Trojan, poses a significant threat to computer security by opening backdoors that allow attackers remote access to systems. This access

In the digital era, providing secure internet access in educational environments is paramount, necessitating robust authentication processes to safeguard sensitive data and comply with legal
Deploying services using open-source software is cost-effective but requires meticulous attention to security. It’s imperative to download software from reputable sources and follow best configuration

Implementing robust access control strategies is vital for safeguarding data and file systems within an organization. This approach not only facilitates operational efficiency but also

In the realm of wireless networking, understanding the security features of various technologies is crucial. The IEEE 802.11 standards, including a/b/g/n variants, form the backbone
In today’s interconnected world, implementing a comprehensive Human Resources Risk Management Plan is crucial for enhancing organizational security. Such a plan not only fortifies network

Developing a security plan for an organization involves several critical steps, from choosing the right security framework to implementing domain-specific controls. This approach ensures a

Network security is a critical concern for any organization, and understanding which ports are commonly targeted by hackers is essential to safeguarding systems. Some ports

In the vast and interconnected world of network security, possessing a detailed understanding of a network’s architecture is not solely the province of system administrators—it’s

In the digital age, organizations are treasure troves of sensitive information, making them prime targets for cyber threats. Protecting these systems, especially those containing student

Understanding and protecting Personally Identifiable Information (PII) is crucial in today’s digital age, where such data can easily identify an individual. PII encompasses a range

In an era where digital landscapes are continually evolving, the encryption of data stands as a bulwark against the relentless attempts of cybercriminals to breach

In today’s digital age, where threats to network security are increasingly sophisticated, the concept of layered security controls has become paramount for businesses of all

In the financial sector, adhering to U.S. Federal and State compliance laws, such as the Gramm-Leach-Bliley Act (GLBA) and Federal Information Security Management Act (FISMA),

The realm of digital security is a battlefield, constantly evolving and adapting in the face of new threats. Yet, even the most robust cryptosystems can

The Islamic State (IS), also known as ISIS, emerged as a formidable force in the global arena, particularly in 2014, when it captured large territories

In the digital age, data loss can be a catastrophic event for any organization. Implementing a robust backup and recovery plan for Linux systems is

In the aftermath of the September 11 attacks, the United States witnessed a significant shift in the balance between national security and individual freedoms. The

Monitoring network assets through log analysis is a critical aspect of maintaining security and performance. Effective logging helps in identifying and rectifying performance issues and
The USA PATRIOT Act, enacted in the wake of the tragic events of September 11, 2001, significantly extended the Federal government’s authority, impacting the private

Linux celebrated for its open-source nature, grants system administrators the power to customize its kernel. However, the decision to modify the kernel should be approached

In the realm of IT, software management stands as a cornerstone of operational stability and security. Particularly in Linux environments, timely software updates are crucial

Ensuring the security of web and database servers is a pivotal aspect of network administration. Despite the uniqueness of each network, there are universally applicable

Securing a Linux server for file sharing involves meticulous attention to the services it hosts, such as Bind, Apache, and MySQL. These services, while essential,

The Arab Spring, a series of anti-government protests and uprisings, began in 2011, drastically altering the political landscape of the Middle East and North Africa.

In the landscape of network security, bastion hosts serve as fortified gateways between the Internet and an organization’s internal network. These hosts require meticulous configuration

In the realm of Linux system administration, employing a layered security strategy is fundamental to defending against potential compromises. While firewalls serve as the primary
In a Linux server environment, securing file storage is a critical aspect of system administration. Whether it’s to ensure the integrity of archived content or

Linux servers offer a range of open-source solutions that can match or exceed the capabilities of Windows server solutions. Choosing the right software is crucial

Linux’s robustness as an operating system is partly due to its comprehensive user permission system. Assigning appropriate permissions is crucial to ensure operational efficiency and

Virtualization has revolutionized server management and security, isolating services within virtual machines (VMs) to protect them from cybersecurity threats. While Linux can run on Windows-based

Linux, renowned for powering many of the world’s busiest web servers, is not immune to security vulnerabilities. Despite its open-source nature, Linux systems require rigorous

In the intricate world of software development, integrating new applications into a corporate network demands a strategic approach to mitigate security risks. Whether commercial or

In the digital landscape, web server applications are often targets for malicious attacks. These applications are vulnerable to threats like SQL injection, cross-site scripting, and

Van Halen, a name synonymous with rock legend status, has seen its fair share of changes, particularly in the lead vocalist department. The band’s journey

In the realm of cybersecurity, properly collecting evidence in the event of an incident is crucial, especially if the situation escalates to legal action. Understanding

WAAF 107.3 in Boston is a staple of the American rock scene, with its roots stretching back to the early 1970s. Renowned for its commitment

In the diverse musical landscape of the 1990s, two artists stood out for their distinctive sounds and cultural impact: Nirvana, the epitome of grunge rock,

The late eighties to early nineties was a transformative period for metal music, epitomized by Metallica’s iconic track “…And Justice For All.” This era marked

The Microsoft Baseline Security Analyzer (MBSA), once a staple tool for security auditing in environments lacking Microsoft Update or local WSUS/SCCM servers, has been deprecated.

In the digital age, ensuring business continuity necessitates a robust backup and recovery plan to swiftly address data loss from various threats like malware outbreaks,

Malware, encompassing adware, ransomware, trojan horses, worms, and viruses, poses a significant threat to computer systems globally. To safeguard an organization, a comprehensive malware management

Group Policy Objects (GPOs) are essential tools within Active Directory environments, offering a structured approach to managing user and computer settings across a network. Implementing

Implementing Role-Based Access Control in a DOMAIN Environment Transitioning from a WORKSTATION-based to a DOMAIN-based environment represents a significant shift towards improved productivity and manageability

Active Directory (AD) stands out as a pivotal element in modern IT infrastructure, providing a robust solution for managing network resources, workstations, and security in

In the realm of healthcare, the protection of patient information is not merely a matter of ethical responsibility but a legal mandate. The Health Insurance

In the healthcare sector, the security of information technology infrastructure is not just a requirement but a cornerstone of patient trust and regulatory compliance. The

Google, a global tech giant, exemplifies the essence of corporate responsibility through its straightforward yet profound principle: “Don’t be evil“. This guiding axiom underpins Google’s

In America today, heart disease remains the leading cause of death, a stark reminder of its deadly grip on our nation’s health. Yet, amidst these

In today’s digitally connected world, the ability for employees to work remotely via Virtual Private Networks (VPNs) is not just a convenience but a necessity

In any organization, the creation of user policies is a nuanced process that necessitates a deep understanding of the various employee roles and their specific

In the complex landscape of healthcare regulation and information technology, organizations face the challenge of aligning their internal IT controls with both legal requirements and

In the intricate landscape of financial information security, the Gramm-Leach-Bliley Act (GLBA) emerges as a critical regulatory benchmark, mandating firms to actively secure customer financial

In the rapidly evolving world of healthcare, ensuring the security and privacy of patient data is not just a priority; it’s a mandate. For organizations
Merging two organizations with distinct corporate cultures and operational structures is a formidable task, particularly in the healthcare sector where compliance with regulations like HIPAA

In the digital age, safeguarding sensitive information and assets is paramount, especially for financial institutions governed by regulations such as the Gramm-Leach-Bliley Act (GLBA). This
From First Bite to Final Absorption: Unraveling the Complex Process The act of eating, especially when it involves a delicious cheeseburger, is not just a

In the aftermath of the September 11 terrorist attacks, the United States witnessed significant legislative changes, notably the introduction of the Patriot Act. Designed to

The Senate Committee on Appropriations stands as a cornerstone of legislative authority in the United States Senate. Tasked with a critical role in the federal

Pregnancy is a journey filled with joy, anticipation, and profound responsibility, particularly when it comes to nutrition. Expecting mothers carry the crucial task of not

In the vast digital expanse of our interconnected world, the ethical quandaries posed by online piracy strike a dissonant chord within the music industry. Brandon

In our increasingly interconnected world, online piracy presents a significant challenge, especially for the music industry. Brandon Gaille (2017) highlights the gravity of this issue,

In our rapidly evolving digital landscape, where information traverses the globe in seconds, active engagement in the U.S. political system is surprisingly on the wane.

Despite being centuries old, the U.S. Constitution is far from outdated. It was crafted with remarkable foresight, providing a framework for a resilient government while

In today’s digital age, the protection of children on the internet is a paramount concern for educational institutions. It’s essential to understand the current regulations

The U.S. presidential election is an intense and competitive affair, with the victor leading not just the nation, but symbolically the free world. However, the

The U.S. Constitution doesn’t mandate a two-party system, yet American politics has gravitated towards this duopoly, maintained by the parties in power. The exclusion of

In the intricate landscape of the United States Constitution, the Fourth Amendment stands as a beacon of protection for citizens, safeguarding their right to privacy.

In an era where digital threats loom large, understanding the underpinnings of cybercrime is crucial for organizations across the board. The Verizon Data Breach Investigations

In the United States, the Constitution guarantees certain freedoms, but the digital age has ushered in complexities concerning privacy expectations. Many Americans are unaware of

Iron plays a pivotal role in our health, being a crucial component of a well-rounded diet for both children and adults. Understanding the sources of
Understanding the Threat Landscape In the complex web of business information technology, social engineering attacks stand out for their cunning exploitation of human vulnerabilities rather

A Comprehensive Approach to Safeguarding Credit Card Transactions In the digital era, accepting credit card payments is a necessity for businesses looking to provide convenience

A Closer Look at Major Cybersecurity Incidents In the digital age, data breaches have become a frequent headline, with some incidents so vast in scope

Unraveling the Web of the Early Internet The Internet, a ubiquitous presence that has transformed every facet of modern life, did not emerge fully formed.

Demystifying How the Internet Works The Internet, an indispensable tool in our daily lives, seamlessly connects us to a world of information, entertainment, and communication.

A Comprehensive View of Network Management Network management extends far beyond the realm of installing software to monitor and report on a network’s performance. This

Exploring the Flexibility in Local Area Network Design Local Area Networks (LANs) embody the nerve center of modern businesses, evolving as dynamically as the companies

Navigating the Complex Terrain of Network Planning The task of designing a network is a complex puzzle, intricately linking budgetary constraints and technical requirements. These
Routing protocols are the unsung heroes of the internet and internal networks, providing the guidelines that allow routers to effectively communicate and determine the best
In the intricate world of networking, understanding the distinctions between routers and switches is fundamental. According to TechTarget, a router is essentially the gatekeeper of
In the vast landscape of networking, understanding the nuances of collision domains is crucial for optimizing performance and efficiency. At the heart of this discussion
In the expansive realm of computer networking, the spotlight often lands on a critical yet sometimes overlooked component: the network switch. Defined by Wikipedia as
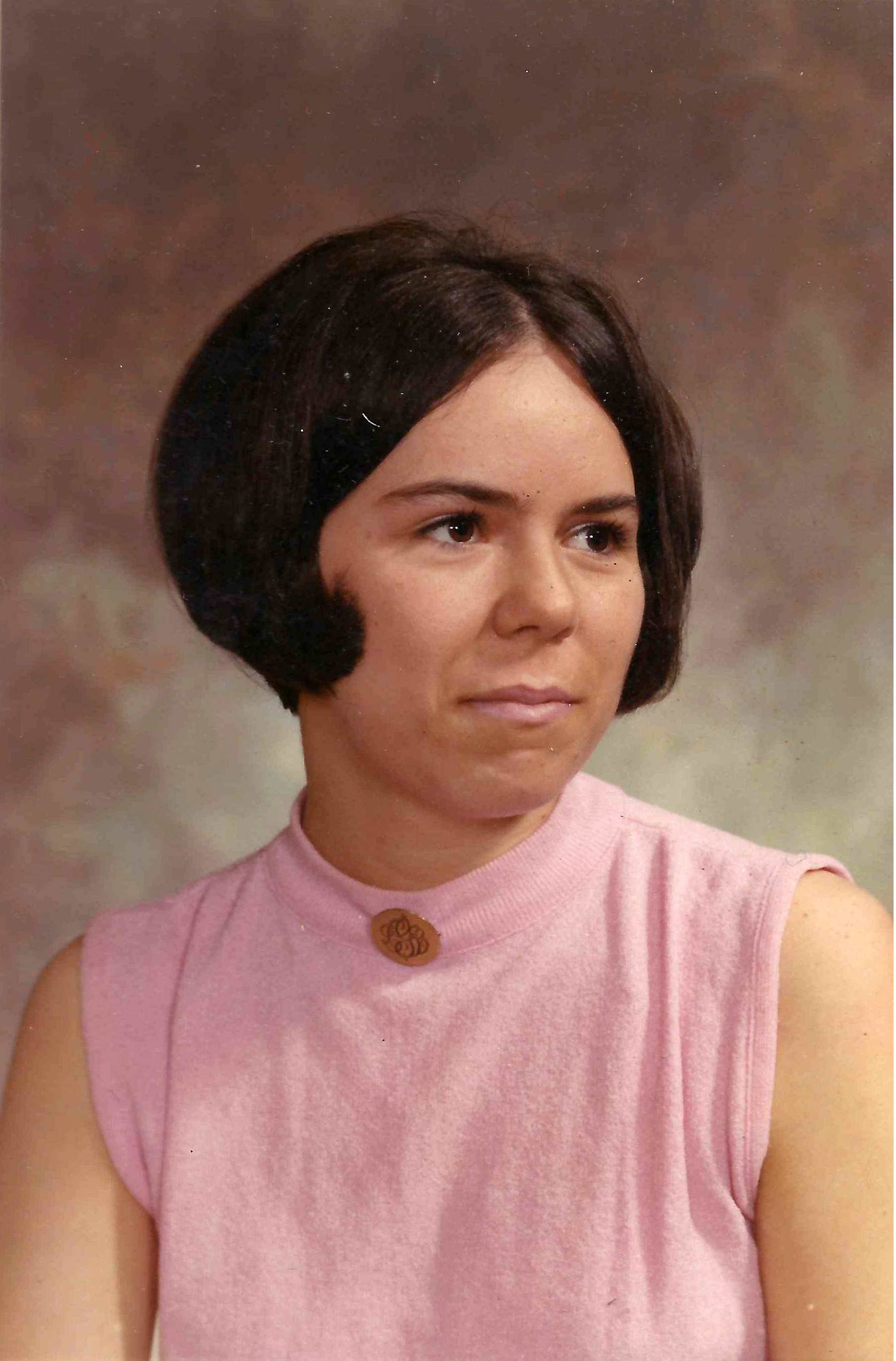
EASTFORD, Linda (Glass) Hopkins of Millbridge Road, Eastford Connecticut passed away on May 19, 2013, under hospice care, surrounded by her loving family, after a